Can You Hack a Computer by Just Knowing the Ip Address and Mac Address?
If yous have been using the Windows operating system for a while, y'all might be well enlightened of CMD or Command Prompt. Information technology's one of the well-nigh powerful tools in Windows, which is used to operate a wide range of tasks. It'due south a command-line interpreter that can be used to access the core features of Windows.
Command Prompt is indeed a useful feature, but hackers often utilize it for the incorrect purpose. Security experts as well use the command prompt to detect potential security loopholes. So, if you are willing to become a hacker or security expert, this mail service might help you.
Also Read: How To Remove Reckoner Viruses Using CMD
List of 10 Best CMD Commands Used In Hacking
In this article, we will share some of the all-time CMD commands that are widely used for Hacking purposes. So, let'southward check out the list of best CMD commands for Windows ten computers.
1. ping
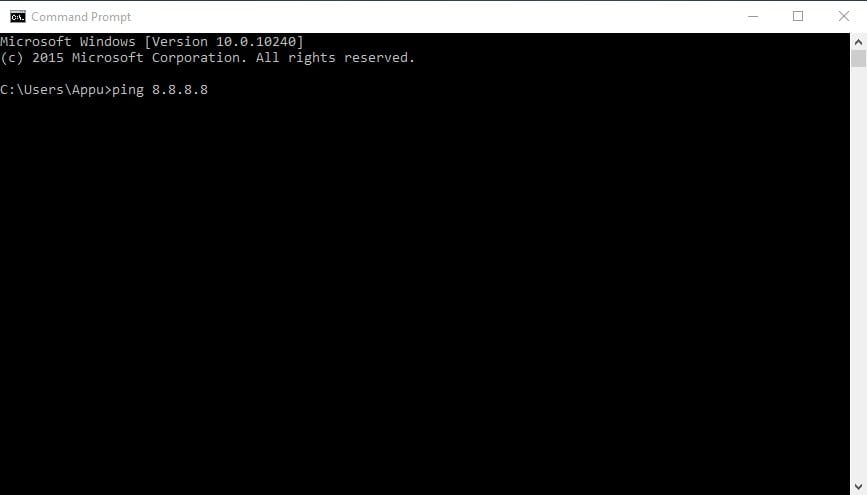
This command uses your cyberspace connection to transport some packets of data to a specific spider web address so these packets are sent back to your PC. The test shows the time it took to accomplish the specific address. In simple words, it helps you to know if the host you are pinging is alive.
You tin use the Ping command to verify that the host computer tin can connect to the TCP/IP network and its resources.
For example, you can blazon in Command prompt ping viii.viii.8.viii, which belongs to Google.
You tin can supervene upon "8.viii.viii.viii" with "www.google.com" or something else yous desire to ping.
two. nslookup
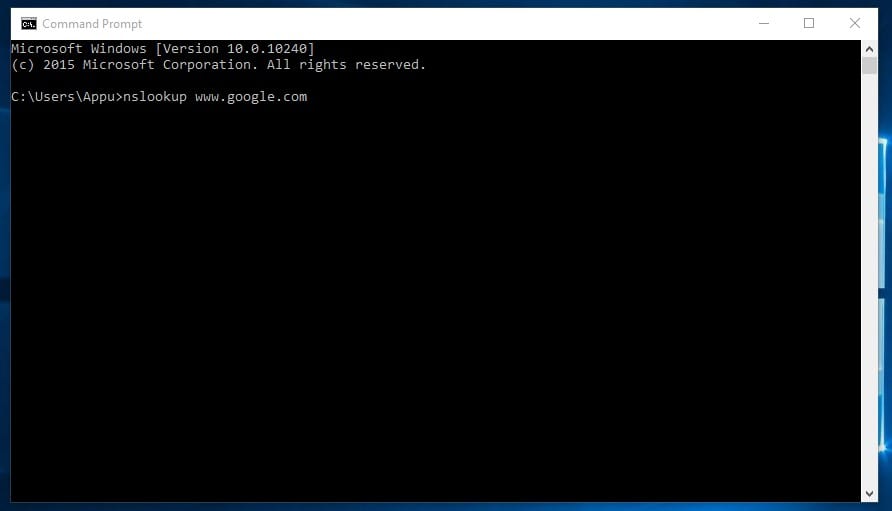
Information technology is a network administration command-line tool that helps you obtain domain proper name or IP accost mapping for any specific DNS tape. Suppose you have a website URL simply want to know its IP Address. Yous tin type in CMD
nslookup www.google.com (Replace Google.com with your website URL of which you want to notice the IP address)
3. tracert
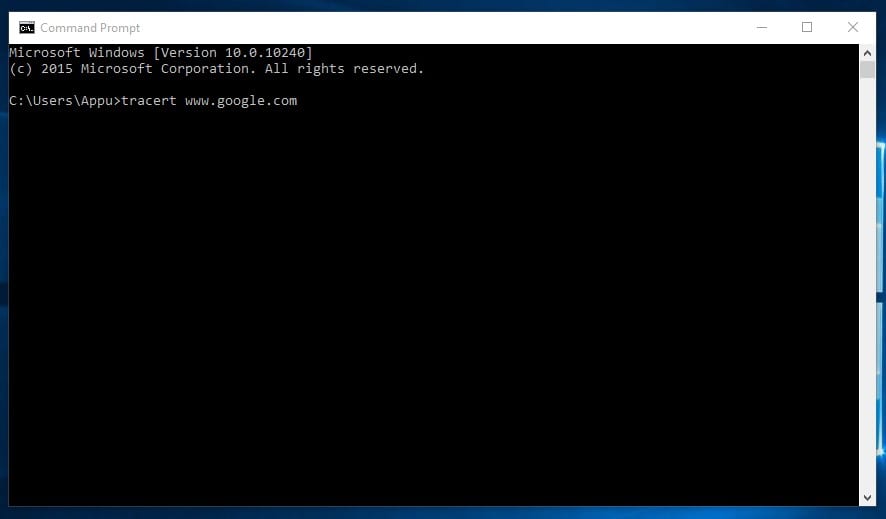
Yous can say Trace Road. Like its proper name, it allows users to trace the route an IP has taken to reach a destination. The command calculates and displays the amount of time each hop took to accomplish a destination. Yous need to type
tracert x.10.x.10 (if yous know the IP Address) or else you can type tracert world wide web.google.com (If you don't know the IP address)
four. arp
This command helps you lot to modify the ARP enshroud. You tin can run an arp-a command on each estimator to run across whether the computers have the correct MAC accost listed for each other to ping each other succeed on the same subnet.
This command as well helps users find out if anyone has washed arp poisoning in their LAN.
Yous can try typing arp-a in the command prompt.
five. ipconfig
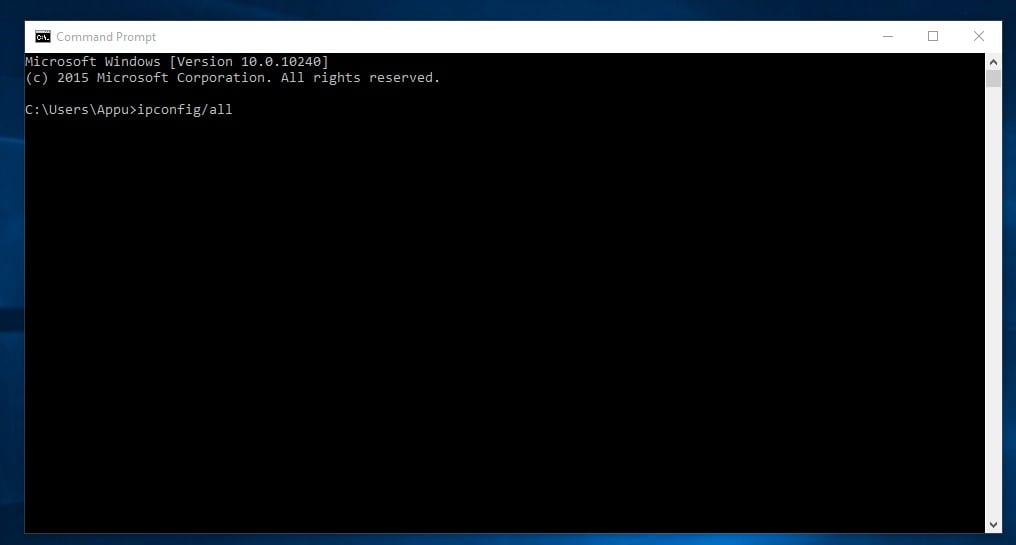
This is the command which shows every useful thing. Information technology will evidence you the IPv6 address, temporary IPv6 accost, IPv4 accost, Subnet Mask, Default gateway, and all other things yous want to know.
You lot can type in the command prompt "ipconfig" or "ipconfig/all"
6. netstat
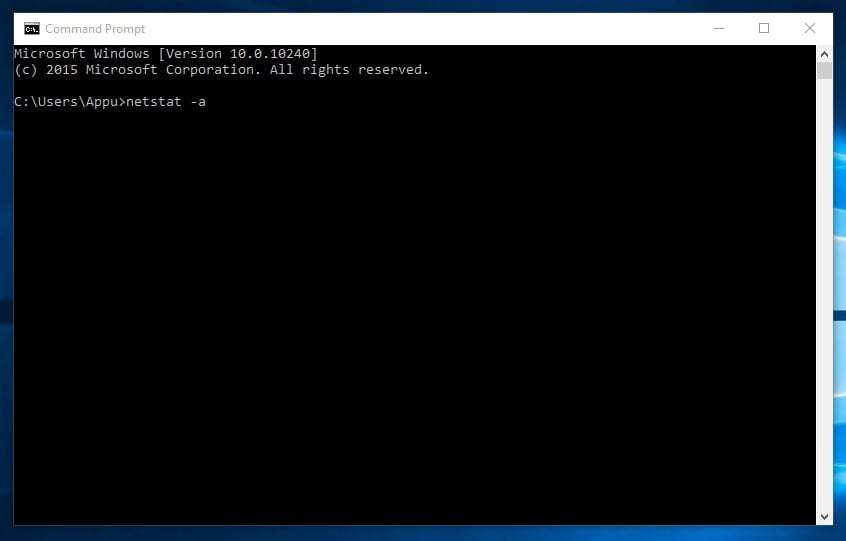
If you want to observe out who is establishing a connection with your computer, you might try typing in the command prompt "netstat -a". It volition display all the connections and get to know well-nigh the active connections and listening ports.
Type in command prompt "netstat -a"
vii. Route
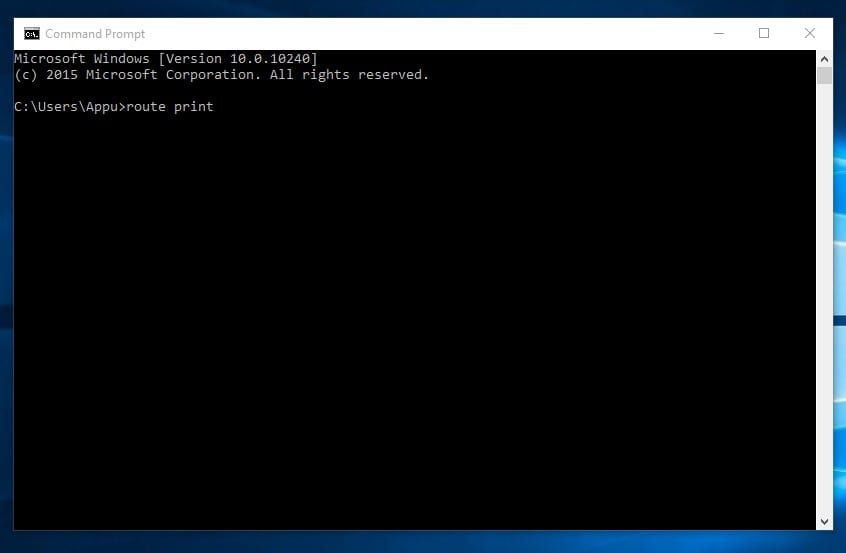
It is a control used to view and manipulate the IP routing table in the Microsoft Windows operating arrangement. This command will show you the routing tabular array, metric, and interface.
You lot can blazon in control prompt "route print"
8. Internet View
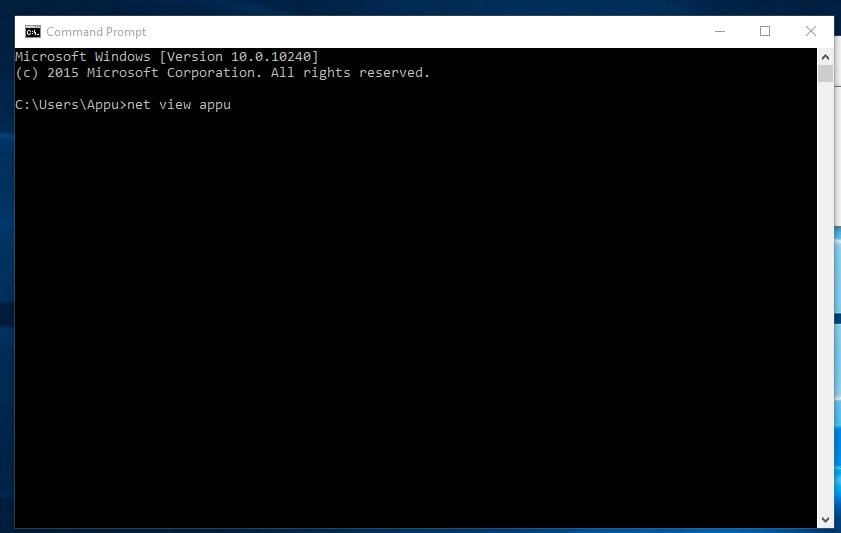
This command displays the whole list of resource, computers, or domains shared by the specified figurer.
You tin blazon in command prompt "net view ten.x.x.ten or computername"
9. Tasklist
This command opens upward an entire chore managing director on the command prompt. Users need to enter the tasklist on CMD, and they will see the list of all running processes. You can figure out all the wrongs with these commands.
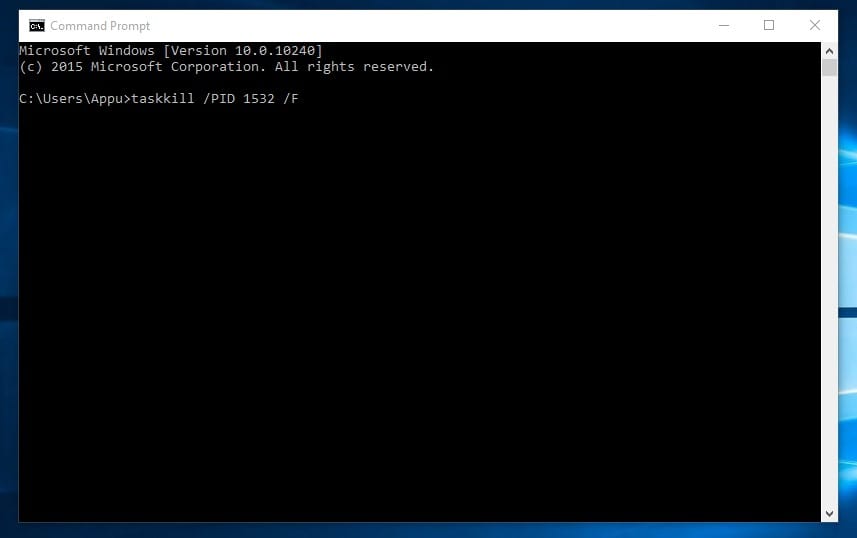
Moreover, the command can also be used to close any process forcefully. For example, if you desire to kill PID 1532 procedure, then you tin enter the control:
taskkill /PID 1532 /F
10. Pathping
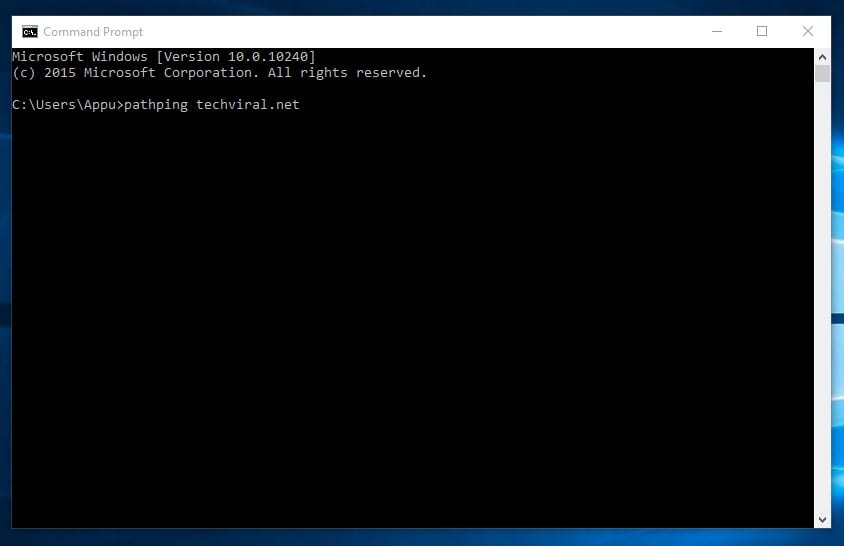
Well, pathping control is pretty much like to the tracert, but it shows more detailed information. The commands take a few moments to complete equally information technology analyzes the route taken and computes bundle loss. On Windows command prompt, type in the following command
pathping techviral.net (Supervene upon techviral.internet with the ane that you want to ping)
And then, above are the best CMD commands used in hacking. Y'all can explore more than than this; we have listed the All-time CMD commands in one of our manufactures! I promise you similar the post! Please share information technology with your friends likewise. Leave a comment beneath if you want to add any control to the list.
Source: https://techviral.net/best-cmd-commands-used-hacking/
0 Response to "Can You Hack a Computer by Just Knowing the Ip Address and Mac Address?"
Post a Comment